What is Cloud Computing? Everything You Need to Know

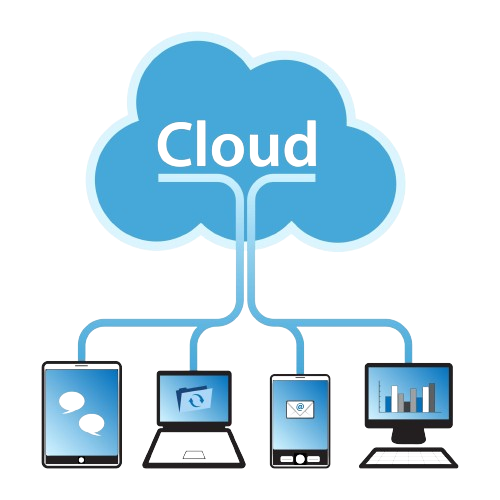
In today’s digital age, cloud computing has become an integral part of our daily lives, revolutionizing the way businesses operate and individuals access data and applications. From storing photos on your smartphone to running complex business applications, cloud computing powers numerous aspects of modern technology Everything you need to know. But what exactly is cloud computing, and how does it work?
Introduction to Cloud Computing
Definition
Cloud computing refers to the delivery of computing services, including storage, servers, databases, networking, software, and Know more, over the internet. Instead of owning physical hardware or infrastructure, users can access these resources on-demand from cloud service providers.
Evolution of Cloud Computing
The concept of cloud computing has evolved over the years, with roots tracing back to the 1960s when the idea of “time-sharing” allowed multiple users to access a single computer simultaneously. However, it wasn’t until the 2000s that cloud computing gained widespread adoption with the emergence of companies like Amazon Web Services (AWS), Google Cloud Platform (GCP), and Microsoft Azure.
Components of Cloud Computing

Infrastructure as a Service (IaaS)
IaaS provides virtualized computing resources over the internet, including virtual machines, storage, and networking. Users can rent these resources on a pay-as-you-go basis, eliminating the need for upfront infrastructure investments.
Platform as a Service (PaaS)
PaaS offers a platform allowing developers to build, deploy, and manage applications without worrying about underlying infrastructure. It provides tools and frameworks for application development, simplifying the development process and accelerating time-to-market.
Software as a Service (SaaS)
SaaS delivers software applications over the internet on a subscription basis. Users can access these applications through a web browser, eliminating the need for installation and maintenance. Examples include email services like Gmail, productivity suites like Microsoft Office 365, and customer relationship management (CRM) software like Salesforce.
Benefits of Cloud Computing
Cost Efficiency
Cloud computing eliminates the need for upfront infrastructure investments and Know allowing businesses to pay only for the resources they use. This pay-as-you-go model reduces capital expenditures and enables cost optimization.
Scalability
Cloud computing offers scalability, allowing users to scale resources up or down based on demand. Whether it’s increasing server capacity during peak traffic or scaling down during off-peak hours, cloud providers offer flexible scaling options to meet changing business needs.
Flexibility
Cloud computing provides flexibility, enabling users to access resources from anywhere with an internet connection. Whether you’re working from home, traveling, or collaborating with team members across the globe, cloud services offer seamless accessibility.
Common Cloud Computing Models

Public Cloud
Public cloud services are provided by third-party vendors over the internet, accessible to multiple users on a shared infrastructure. Examples include AWS, GCP, and Azure, offering a wide range of services to businesses and individuals alike.
Private Cloud
Private cloud services are dedicated to a single organization, offering greater control, security, and customization. While they may require higher upfront investments, private clouds provide enhanced privacy and compliance capabilities, making them ideal for industries with strict regulatory requirements.
Hybrid Cloud
Hybrid cloud environments combine public and private cloud infrastructure, allowing organizations to leverage the benefits of both models. This hybrid approach offers greater flexibility, scalability, and data deployment options, enabling businesses to optimize performance and cost-effectiveness.
Security Concerns in Cloud Computing

Data Privacy
Data privacy is a major concern in cloud computing, as storing sensitive information on third-party servers raises questions about confidentiality and compliance with data protection regulations. Cloud providers implement stringent security measures to safeguard data against unauthorized access and breaches.
Compliance
Compliance with industry regulations and standards is essential for businesses operating in regulated sectors such as healthcare, finance, and government. Cloud providers offer compliance certifications and adherence to regulatory requirements, ensuring data protection and legal compliance.
Cybersecurity Threats
Cybersecurity threats such as malware, phishing attacks, and data breaches pose significant risks to cloud infrastructure and data. Cloud providers employ advanced security measures such as encryption, multi-factor authentication, and intrusion detection systems to mitigate these threats and protect customer data.
Adoption of Cloud Computing
Industries Leveraging Cloud Computing
Various industries, including healthcare, finance, retail, and manufacturing, are increasingly adopting cloud computing to streamline operations, improve agility, and drive innovation. From electronic health records in healthcare to online banking services in finance, cloud technology is transforming traditional business models.
Small and Medium-sized Enterprises (SMEs)
Cloud computing levels the playing field for small and medium-sized enterprises (SMEs), enabling them to access enterprise-grade infrastructure and services without the need for significant upfront investments. Cloud solutions offer SMEs scalability, affordability, and competitiveness in the digital marketplace.
Future Trends in Cloud Computing

Edge Computing
Edge computing brings computing resources closer to the data source, reducing latency and enabling real-time processing for mission-critical applications. With the proliferation of Internet of Things (IoT) devices and 5G networks, edge computing is poised to revolutionize industries such as manufacturing, healthcare, and autonomous vehicles.
Artificial Intelligence (AI) Integration
AI integration in cloud computing enables intelligent automation, predictive analytics, and personalized experiences. Cloud providers offer AI-powered services such as machine learning, natural language processing, and computer vision, empowering businesses to derive insights, optimize processes, and drive innovation.